Category: Azure
-
Azure Shared Disks are coming!!!
Do you still have a need or desire to continue to run your SharePoint environment in an on-premises data center so that you can have them luxury of Always On Availability Groups with SQL Server? Well… now you can really take that workload to the cloud (with some minor caveats) once Microsoft fully goes GA…
-
Azure: Public Preview of Serial Console
I have to say that this is crazy that Microsoft Azure now supports a Serial Console for Virtual Machines (at least in Public Preview). Check out the blog entry over here – https://azure.microsoft.com/en-us/updates/azure-serial-console/ I decided to give it a little try to see more and it works like a champ. Very cool to see this capability…
-
Azure: Setting up a custom domain for Office 365 by way of Azure Active Directory
If you’re like me, sometimes you like to do things a little more efficiently and elegantly through PowerShell or through the Azure portal when it deals with the underlying infrastructure that’s associated with an Office 365 tenant. If you’re using Office 365 you’ve established a tenant with a .onmicrosoft.com name. Reminder PSA: You can’t change…
-
Office 365: Managing your users through PowerShell
If you’re like me, then you tend to find yourself wanting to automate as much as possible, or at least be able to work with sets of data in a way that quickly allows you to get to the root of an issue rather than clicking through endless screens of information. In case you were…
-
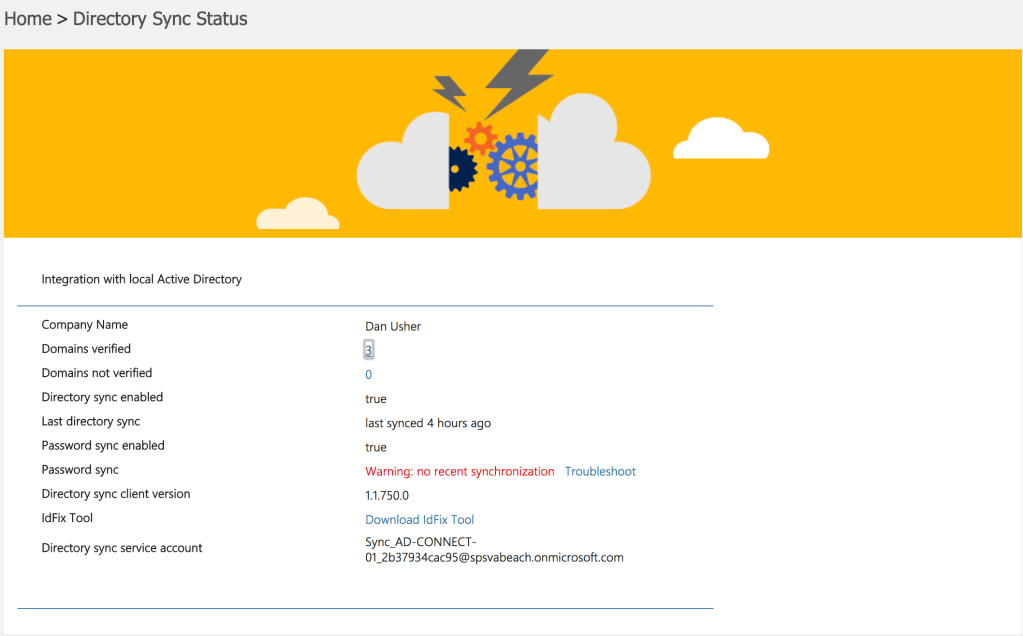
Don’t turn into a pumpkin because of DirSync with your Office 365 system
I feel like I may have already mentioned this on the Twitter, but I feel like I need to put out a reminder PSA for folks that perhaps were asleep at the terminal or looking at their iPhone playing Pokemon Go… DirSync and AzureAD Sync Service will no longer connect as of 1 January 2018.…
-
Azure’s Access Control Services Retiring
If you’ve been working with Azure for a while you may have come across a need to make use of Azure’s Access Control Services. This service offering or capability effectively allowed developers to create something that was hosted on Azure but have authentication and authorization to be completed performed outside of the application that a…
-
Office 365 Group Management and Auto-Expiration Public Preview
If you’ve been working with Microsoft SharePoint Products and Technologies, you probably remember a utility that was made available as a part of SharePoint Server 2003 to automatically delete old site collections that hadn’t been worked with in a while. This was an incredibly helpful utility for system administrators that were watching their SharePoint systems…
-
Azure QuickStart Templates
If you’re like me you prefer to automate things as much as possible. In some instances that means using desired state configuration, in other instances it’s launching a series of PowerShell scripts. This saves time and helps to ensure a configuration that’s repeatable and easy to kick off without a ton of work – yes…
-
ARM Template Reference Now Available
If you’ve been tracking Microsoft’s Azure cloud offering over the past few years you’ve probably noticed that there have been a few (hundred) changes during that time period. And by hundred, I mean multiple hundreds. . . One of those changes was to transition from the Azure Service Management interfaces to the Azure Resource Management…